In addition to groups, user accounts are subject to constant changes. In particular, the accounts of employees who have left the company pose a major threat. Unauthorized access to the internal network should
be avoided.
Identify obsolete user accounts
This analysis returns a list of all user accounts, their status, and their last login. On this basis, all accounts can be quickly identified that seemingly can no longer be used and thus deactivated. "
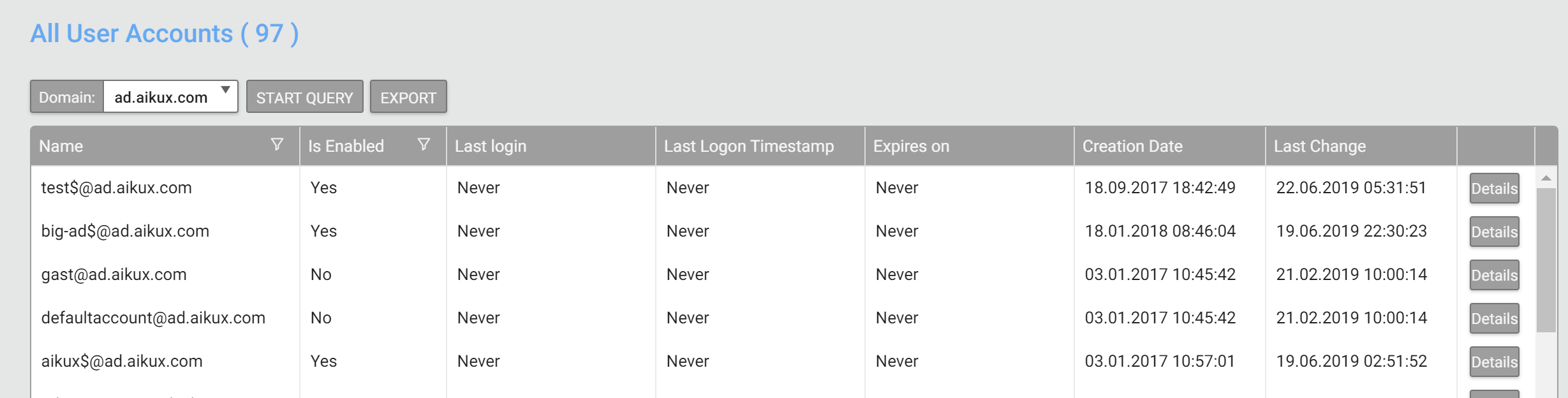
For easy reuse, this report can be exported as an Excel file.
Recommendation: compare this list regularly with the HR department. Better still would be the introduction of an IAM system
which ensures that accounts are automatically deactivated or deleted after an employee leaves the company.

